Every day, thousands of people use erome to enjoy free photos and videos Onlyfans is the social platform revolutionizing creator and fan connections Come share your amateur horny.
Explain Honeypot In Network Security at Lawrence Henry blog
Honeypot__thot u/honeypot__thot 531 karma · joined 4 yr
Ago follow chat overview posts comments
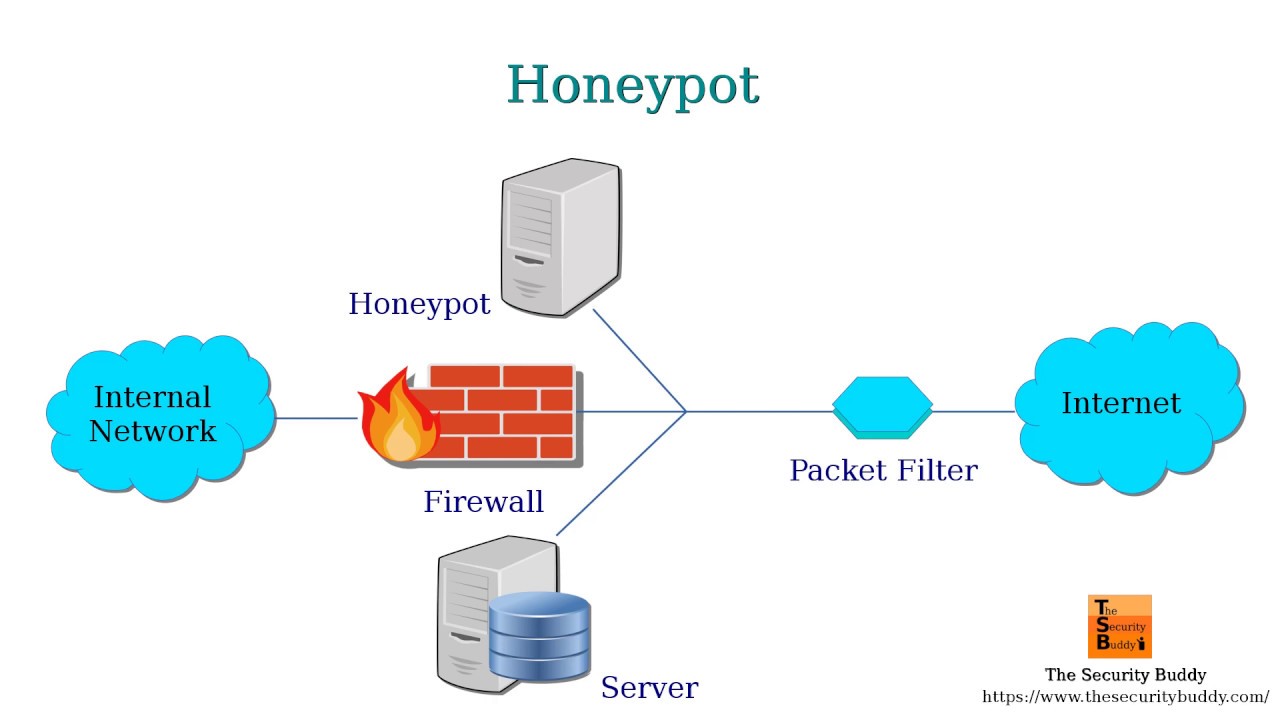
Dave rubin of the rubin report shares a dm clip about kash patel launching an investigation into former fbi director james comey's plot to use honeypot female agents to entrap donald trump Cause honeypot operated by sk shielders it is said that automatic login was set up for employee emails in the virtual machine environment, and the hacking occurred through that route # sk shielders explained that only honeypot information was leaked to induce attackers in the early stages of the incident, but it was later confirmed that actual data had been leaked, and the hacking damage. In cybersecurity and law enforcement contexts, a honeypot is a system or resource that appears to be a legitimate target for criminal activity but is in fact controlled or monitored by investigators